Types of PR comments
Endor Labs generates the following types of PR comments based on the nature of the findings in a scan:- PR comments for Secrets: For findings of type
FINDING_CATEGORY_SECRETS, Endor Labs adds a comment directly on the specific line where the secret is detected, using the line number provided in the finding object. These comments remain visible even if the secret is removed in a later scan. - PR comments for SCA: For SCA findings, Endor Labs adds a single comment that applies to the entire PR. It summarizes all findings from the policy evaluation results. The comment is updated with each scan run to reflect only the latest findings.
- PR comments for SAST: For findings of type
FINDING_CATEGORY_SAST, Endor Labs adds a single comment that applies to the entire PR. It summarizes all SAST-related policy violations detected during the scan. The comment is updated with each run and reflects only the latest findings.
Enable PR comments
After enabling PR comments, you must Configure an action policy to allow comments to be posted on pull requests or merge requests.GitHub PR comments
You can enable PR comments for GitHub through one of the following methods.GitHub App
You can enable PR comments during the initial setup of the GitHub App or GitHub App (Pro), or by editing an existing integration. Once enabled, Endor Labs automatically adds comments to pull requests when policy violations are detected.GitHub Actions
You can configure GitHub Actions to comment on PRs if there are any policy violations. Make sure that your GitHub Actions workflow includes the following configuration.- The workflow must have a
withclause including:enable_pr_commentstotrueto publish new findings as review comments andgithub_token: ${{ secrets.GITHUB_TOKEN }}. This token is automatically provisioned by GitHub when using GitHub Actions. See GitHub configuration parameters for more information. - To grant Endor Labs the ability to comment on PRs you must include the permission
pull-requests: write.
PR comments example
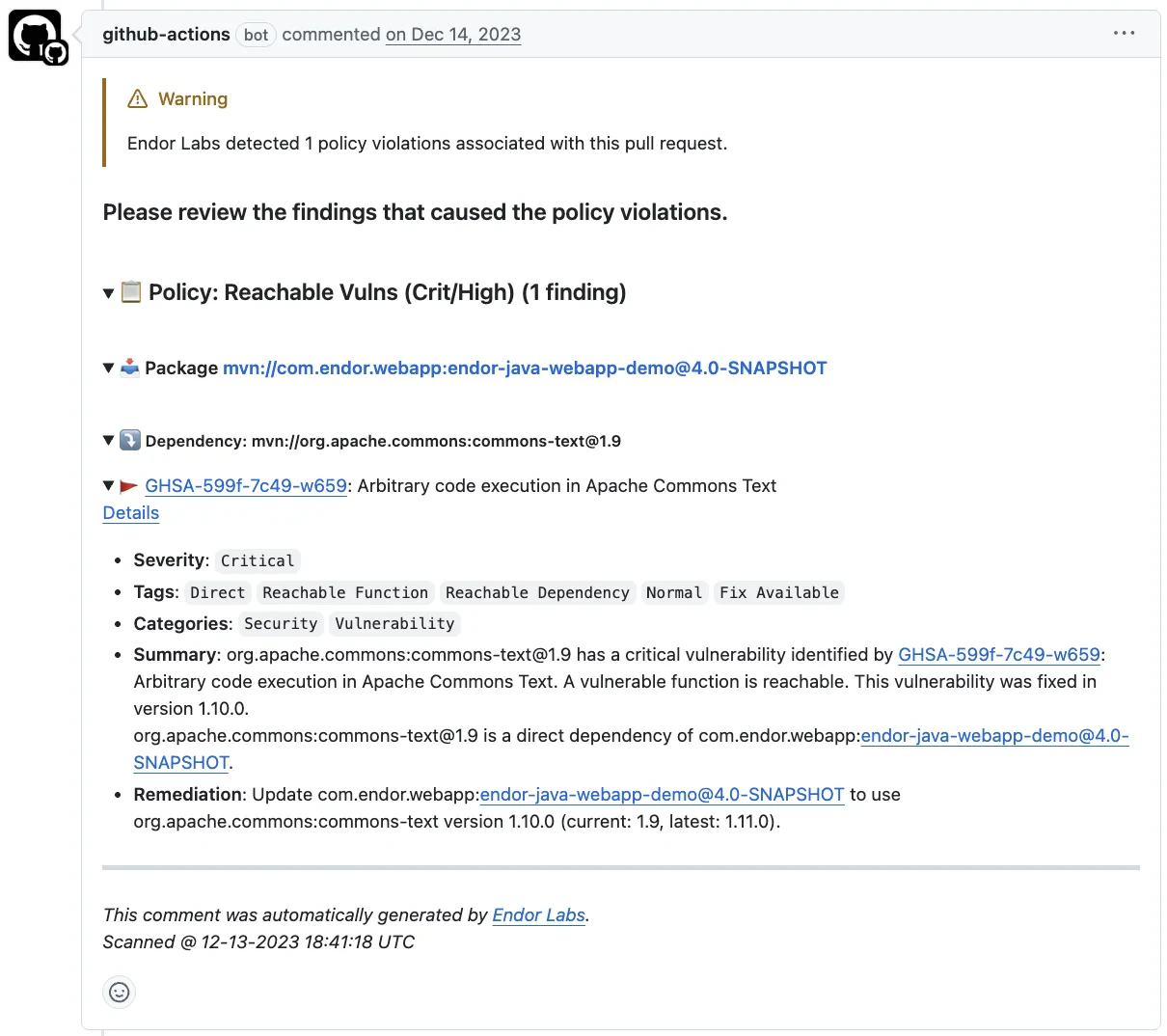
The main.yaml file in this sample repository contains the following configuration to enable PR comments.enable_pr_comments set as true, a comment is added to the PR on the policy violation.
You can expand the comment to view the following details:
- Issue type: Describes the category of the security or policy violation
- Severity: Indicates how critical the issue is.
- Impacted files or dependencies: Specifies the files and packages affected by the issue.
- Remediation steps: Specifies the required fix to resolve the detected issue.
GitHub PR comments with Endor Labs CLI
You can generate PR comments using the CLI by including the following flags in theendorctl scan command.
- Set
--enable-pr-commentsto activate PR comment generation. - Use
--scm-pr-idto specify the pull request to comment on. - Use
--scm-token(or set theENDOR_SCAN_SCM_TOKENenvironment variable) and set thepull-requestspermission towritefor the token.
You can continue to use
--github-pr-id flag, but it will be deprecated and removed in the future.GitLab MR comments
You can enable MR comments for GitLab through one of the following methods.GitLab App
You can enable MR comments during the initial setup of the GitLab App or by editing an existing integration. Once enabled, Endor Labs automatically adds comments to merge requests when policy violations are detected. See GitLab MR comments for more information.GitLab CI pipelines
You can configure GitLab CI pipelines to comment on merge requests when policy violations are detected. Add--enable-pr-comments, --scm-pr-id=$CI_MERGE_REQUEST_IID, and --scm-token=$ENDOR_SCAN_SCM_TOKEN to your scan command. Configure a GitLab CI/CD variable ENDOR_SCAN_SCM_TOKEN with your GitLab personal access token with the api scope. See Enable MR comments for complete configuration examples.
GitLab MR comments with endorctl
You can generate MR comments with endorctl by including the following flags in theendorctl scan command.
- Set
--enable-pr-commentsto activate MR comment generation. - Use
--scm-pr-idto specify the merge request to comment on. - Use
--scm-token. The token takes priority over installation PATs.
Security review comments for GitLab merge requests are not yet supported.
Configure Action policy for PR comments
You must create an Action policy to receive comments on your pull request after enabling PR comments.- Create an Action policy.
- Set the Branch Type to
Pull Requestso the policy applies specifically to pull request scans. - Under Action, select Enforce Policy, then choose:
- Warn to post a comment without breaking the build.
- Break the Build to fail the build and block the pull request.
- Define the scope of the policy using tags. Only projects that match the specified tags will receive PR comments.
Customize PR comments templates
Endor Labs provides a default template with standard information that will be included in your pull requests as comments. You can use the default template, or you can choose to edit and customize this template to fit your organization’s specific requirements. You can also create custom templates using Go Templates.- Select Integrations from the left sidebar.
- Click Edit Template next to GitHub PR comments under Notifications.
- Make the required changes and click Save Template.
PR comments data model
To create custom templates for PR comments, you must understand the data supplied to the template. See the following protobuf specification for theGithubCommentData message that this template uses.
See the following sections to understand the Finding and PackageVersion definitions that are used in this protobuf specification:
See the following specification to understand the additional functions that are also available. You can access these functions by using their corresponding keys.

