- Policy violations in the source code
- Secrets inadvertently included in the source code
- For policy violations, the workflow is designed to either emit a warning or return an error based on your action policy configurations.
- For secrets discovered in the commits, developers can view the PR comments and take necessary remedial measures.
Install Software Prerequisites
To ensure the successful execution of the Endor Labs GitHub action, the following prerequisites must be met:- The GitHub action must be able to authenticate with the Endor Labs API.
- You must have the value of the Endor Labs namespace handy for authentication.
- You must have access to the Endor Labs API.
- If you use keyless authentication, you must set an authorization policy in Endor Labs. See Authorization policies for details.
Secure GitHub Actions with immutable commit SHA
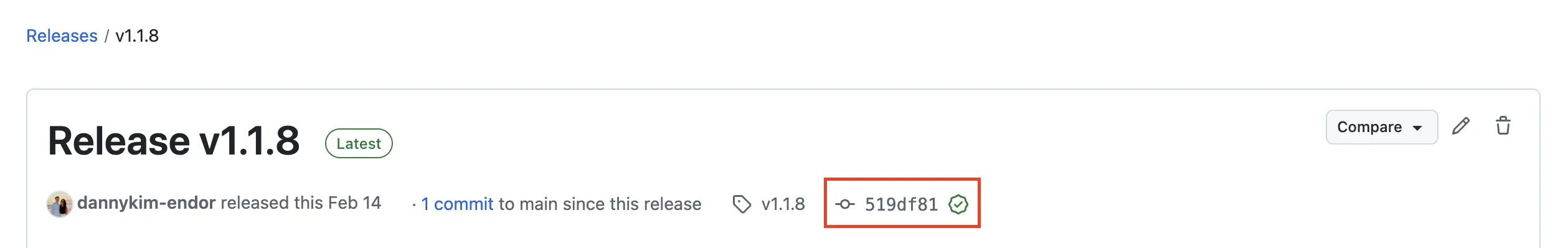
Endor Labs recommends pinning the commit SHA of the GitHub Actions to enhance security. By pinning GitHub Actions to a commit SHA, you make the code immutable even if the tag version is changed or the code is updated. To manually find the Endor Labs GitHub action’s latest commit SHA:- Go to Endor Labs GitHub Actions and select the latest release version in Releases.
-
Click the commit of the release.
-
Copy the commit SHA from the URL.
The commit SHA is the 40-character alphanumeric string in the URL after
/commit/.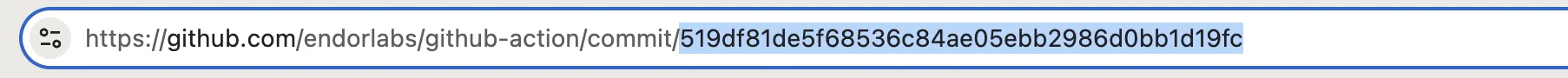
Example GitHub Action Workflow
Endor Labs scanning workflow using GitHub Actions that accomplishes the following tasks in your CI environment:- Tests PRs to the default branch and monitors the most recent push to the default branch.
- Builds a Java project and sets up the Java build tools. If your project is not on Java, then configure this workflow with your project-specific steps and build tools.
- Authenticates to Endor Labs with GitHub Actions keyless authentication.
- Scan with Endor Labs.
- Comments on PRs if any policy violations occur.
- Generates findings and uploads results to GitHub in SARIF format.
Set up branch tracking in GitHub Actions
In Git, a detached HEAD state occurs when the repository checks out a specific commit instead of a branch reference. In this state, Git points the HEAD directly to a commit hash, without associating it with a named branch. As a result, actions performed, such as creating new commits or running automated scans, do not carry branch identity unless explicitly specified. Proper branch context enables Endor Labs to:- Associate scans with the correct branch
- Identify scans on the monitored default branch
- Track findings and display metrics accurately across branches
 GitHub Actions typically maintains proper branch context automatically. However, to ensure scans are properly tracked, when using the Endor Labs GitHub Action, set
GitHub Actions typically maintains proper branch context automatically. However, to ensure scans are properly tracked, when using the Endor Labs GitHub Action, set pr: false to create monitored versions that appear on dashboards. Use if: github.event_name == 'push' to trigger only on pushes to the default branch:
Scan containers with OS reachability
You can use the Endor Labs GitHub Action to scan container images with OS reachability enabled. Container reachability identifies which packages inside a container image are actually used at runtime, helping you prioritize the most critical vulnerabilities for remediation. Setscan_container: true and os_reachability: true to enable container scanning with reachability analysis:
Authenticate with Endor Labs
Endor Labs recommends using keyless authentication in CI environments. Keyless authentication is more secure and reduces the cost of secret rotation. To set up keyless authentication see Keyless Authentication. If you choose not to use keyless authentication, you can configure an API key and secret in GitHub for authentication as outlined in Managing API keys.Authentication Without Keyless Authentication for GitHub
If you are not using keyless authentication for GitHub Actions, you must not provideid-token: write permissions to your GitHub token unless specifically required by a step in this job. You must also set enable_github_action_token: false in your Endor Labs GitHub Action configuration.
The following example configuration uses the Endor Labs API key for authentication:
Endor Labs GitHub Action Configuration Parameters
The following input configuration parameters are supported for the Endor Labs GitHub Action:Common parameters
Endor Labs GitHub Actions supports the following input global parameters:Scanning parameters
The following input parameters are also supported for the Endor Labs GitHub Action when used for scanning:To enable AI SAST analysis, set the
additional_args parameter to --ai-sast-analysis=agent-fallback.Environmental variables
You can use the following environmental variable for the Endor Labs GitHub Action:Artifact scanning parameters
Use the following parameters and the latest sign action to build artifact signing through Endor Labs GitHub Actions. The optional parameters are required only ifenable_github_action_token in common parameters is false. If true (default value), GitHub automatically populates the optional and other parameters as token claims and sends them to Endor Labs.

